This article contains my first writeup on a machine from Hack The Box. If you have not checked out Hack The Box yet, I really suggest you do. Aside from providing classical CTF-style challenges, the plattform hosts plenty of vulnerable machines (boxes), which are supposed to be exploited. The boxes tend to be geared to realistic scenarios and are thus an awesome opportunity to increase your own pen testing skills.
In order to prove the exploitation of a machine, there are two different flag files stored on each machine. The first one to acquire is a file called user.txt, which can be read by a low privileged user. The next step after initially exploiting the machine is to escalate privileges gaining access to an administrative user (root access). With this high privileged user a second file called root.txt can be read. Both files contain a flag (an md5sum), which is supposed to be submitted on the Hack The Box website rewarding you with the corresponding points for this machine.
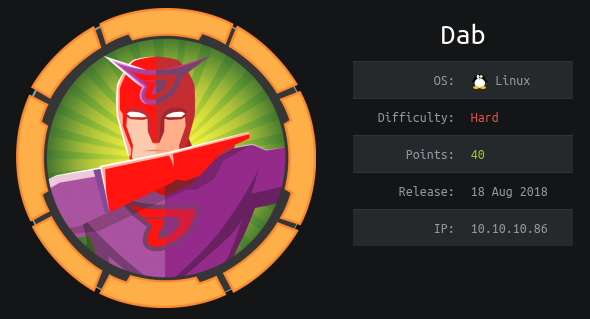
According to those two steps/files the article is divided into the following sections:
→ User
– Port Scan
– FTP (Port 21)
– SSH (Port 22)
– HTTP nginx (Port 80)
– HTTP nginx (Port 8080)
– Back to SSH
→ Root
– Initial Enumeration
– SUID binaries
– myexec
– libseclogin.so
– myexec’s password
– ldconfig
– Compile own shared Library
Continue reading “Hack The Box – Dab”